By John Patzakis
At X1, we believe the future of enterprise AI depends on a simple but often overlooked principle: data should not have to move in order to become intelligent. With the launch of X1 Search v11, we are introducing a fundamentally different approach—one that embeds AI directly into our index-in-place architecture. Rather than forcing organizations to centralize and copy their data into external platforms, we enable AI to operate exactly where that data already lives. You can read the full press release here: https://www.x1.com/x1-introduces-ai-powered-x1-search-delivering-secure-ai-in-place-for-individual-and-enterprise-users/
This release represents an important milestone for us and for our customers. As Chas Meier noted, “X1 Search v11 marks an important milestone in how organizations can safely apply AI…without compromising the security controls enterprise environments demand.” That statement reflects our core design philosophy: AI must adapt to enterprise security, compliance, and governance requirements—not the other way around.
With X1 Search v11, we are delivering AI capabilities directly within our micro-index. That means organizations can apply advanced intelligence—classification, categorization, and contextual analysis—across emails, files, and collaboration data without ever relocating that information. Everything happens in place, within existing security boundaries, whether on endpoints or across enterprise systems.
For large enterprises, this architecture unlocks an even more powerful capability: the ability to deploy their own trained and curated large language models directly into the X1 index. Instead of relying solely on generic, hosted AI services, organizations can operationalize models tailored to their data that reflect their internal policies, regulatory requirements, and business workflows. These models run directly against their data, in place, delivering highly relevant and controlled outcomes.
This approach stands in sharp contrast to traditional hosted AI platforms. In those models, organizations must copy and transfer massive amounts of sensitive data into third-party hosted AI platforms before any meaningful analysis can occur. That process introduces serious risks. Moving data to outside providers complicates compliance, potentially compromises IP, and creates new attack surfaces that most enterprises simply cannot accept.
Beyond security concerns, the traditional model also breaks down operationally at scale. Enterprises are not dealing with small data sets; they are managing dozens of terabytes of distributed, unstructured data. Attempting to duplicate and transfer that volume is not just costly; it is infeasible. The result is delays, fragmentation, and incomplete analysis—undermining the very promise of AI.
We have taken a different path. By bringing AI to the data through our distributed micro-indexing technology, we eliminate the need for data movement entirely. Models can be deployed directly to where data resides, enabling real-time analysis while preserving security, reducing infrastructure overhead, and scaling seamlessly across the enterprise.
We see X1 Search v11 as more than a product release—it is a shift in how enterprise AI is deployed. Organizations no longer have to choose between innovation and control. With AI in place, they can achieve both.
To see this in action, we invite you to join our upcoming live product tour on Thursday, April 23, providing a guided walkthrough of the new AI-enriched capabilities and flexible model deployment features.

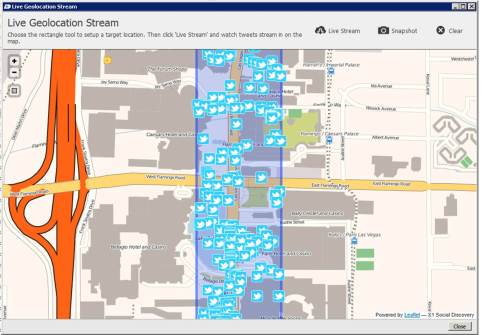
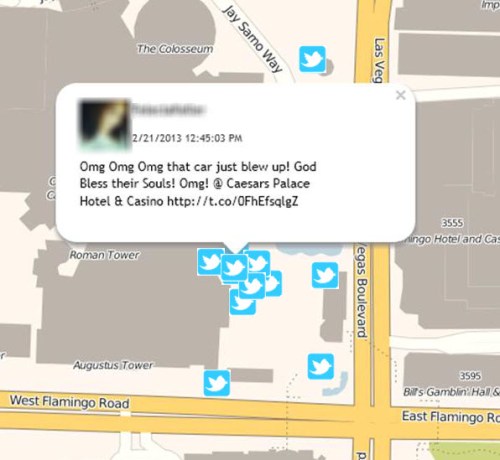
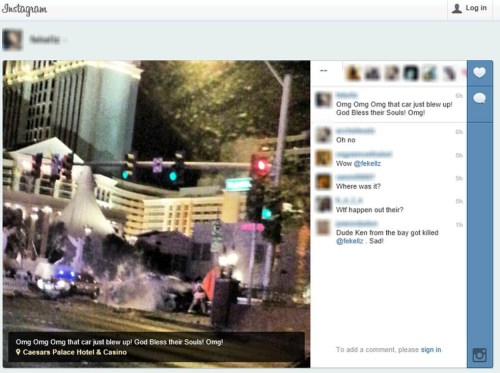



 “leveraging Facebook is just one of many ways law enforcement officials are gleaning evidence from social media to help them solve crimes.” According to a recent survey performed by LexisNexis on federal, state and local law enforcement officials who use social media, 4 of 5 used social media to gather evidence during investigations. Kelly states, “Half said they checked social media at least once a week, and the majority said social media helps them solve crimes faster.”
“leveraging Facebook is just one of many ways law enforcement officials are gleaning evidence from social media to help them solve crimes.” According to a recent survey performed by LexisNexis on federal, state and local law enforcement officials who use social media, 4 of 5 used social media to gather evidence during investigations. Kelly states, “Half said they checked social media at least once a week, and the majority said social media helps them solve crimes faster.”